App信息
包名:com.example.androiddemo
第一关
一个登录界面
把apk丢进jadx进行分析
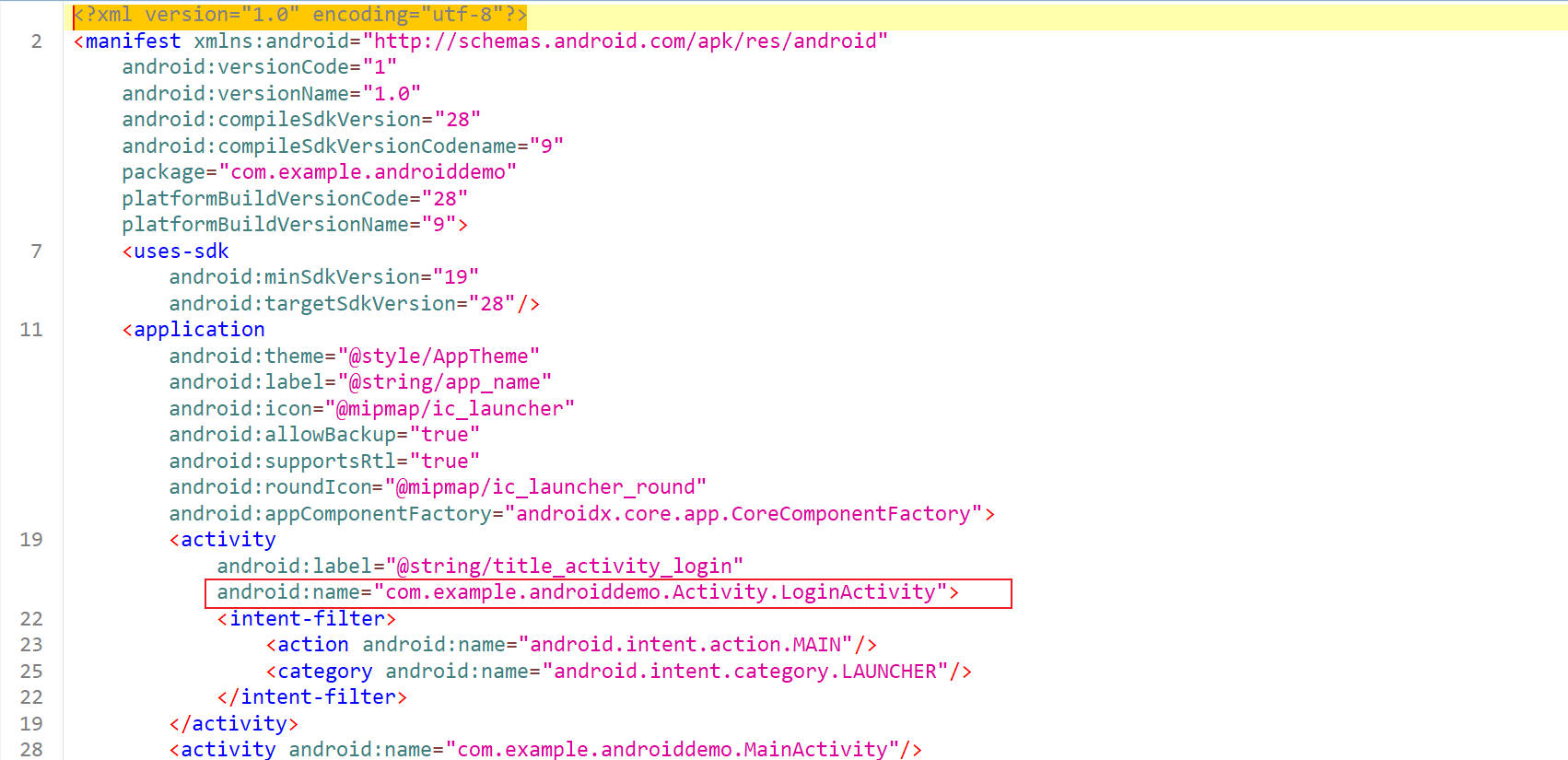
查看AndroidManifest.xml文件
程序启动的第一个Activity是com.example.androiddemo.Activity.LoginActivity
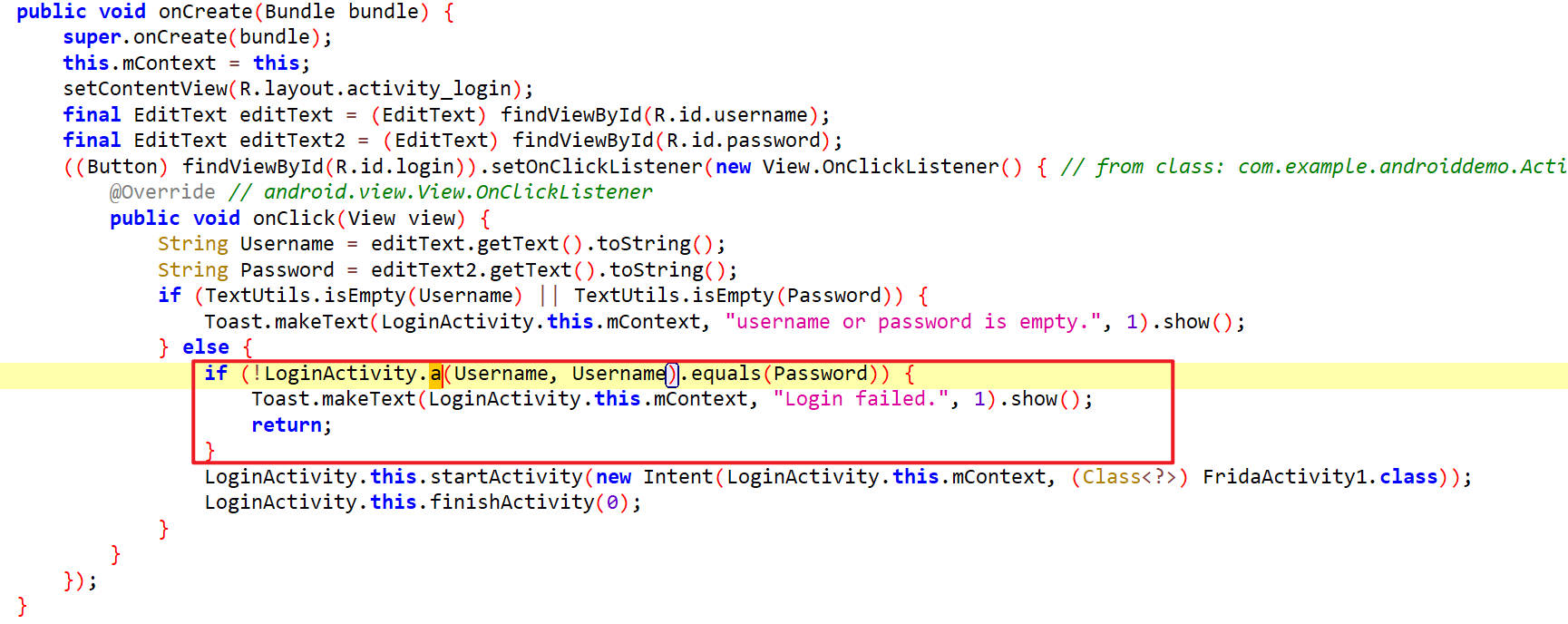
LoginActivity
如下,调用了一个a方法来对用户名和密码进行校验
a
如下,对Username进行了一次HmacSHA256签名
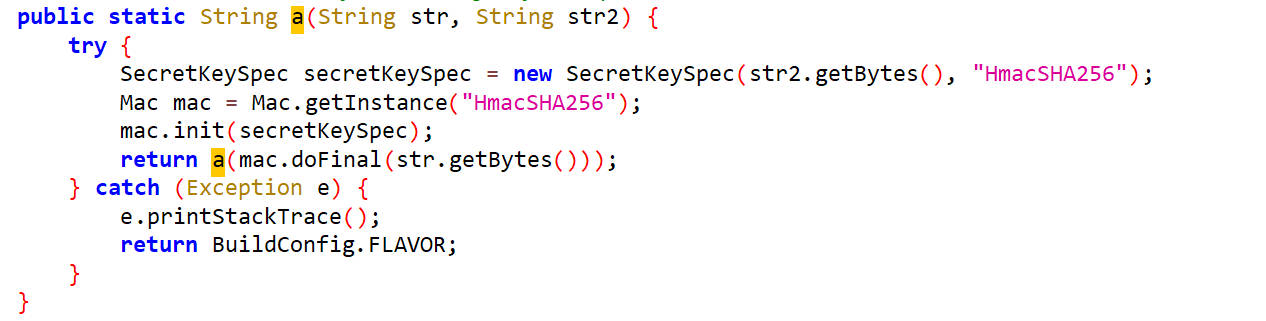
当Username的HmacSHA256签名与Password相同时,可以登录成功。
hook a
1 | function hook_a(){ |
hook 结果
1 | bileton |
输入用户名和密码
登录成功
进入下一关
点击进入下一关,会出现Check Failed
FridaActivity1
查看源码,得知点击登录之后,会进入FridaActivity1

如下是FridaActivity1的内容
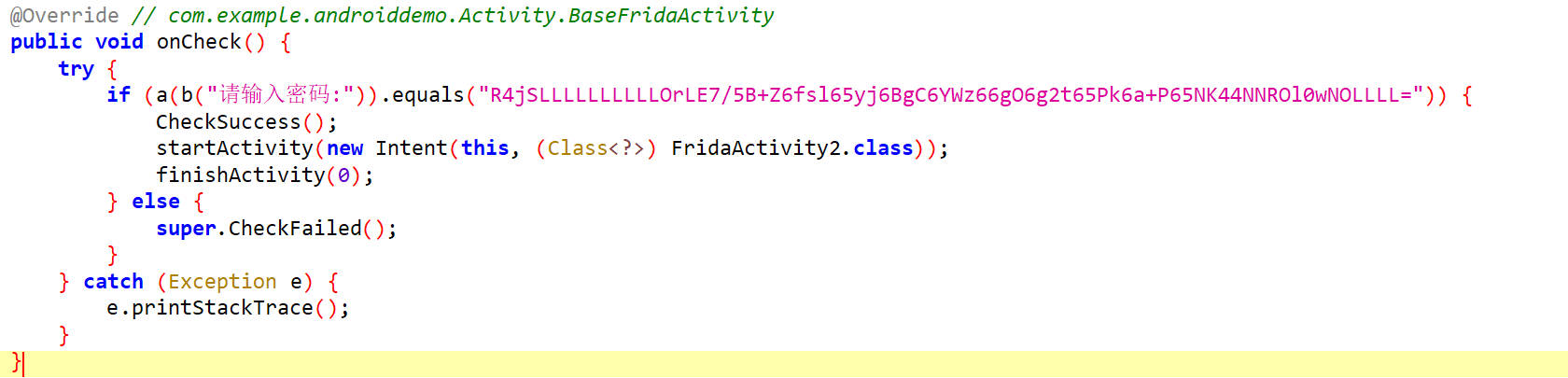
绕过方式很简单,可以直接修改a方法的返回值
1 | function hook_a(){ |
hook 结果
1 | result: R4jSLLLLLLLLLRknplkBpZDpis69kh7i+YAPTmMn2ABsOLLLLL== |
还有另一种绕过方式
1 | function hook_a(){ |
hook 结果
1 | original_data: 31,-117,8,0,0,0,0,0,0,0,123,-79,126,-5,-117,125,-109,-97,-74,46,125,-70,-66,-19,-7,-126,70,43,0,-15,-40,-110,-30,16,0,0,0 |
进入到了第二关
第二关
第一关结束跳转到了FridaActivity2
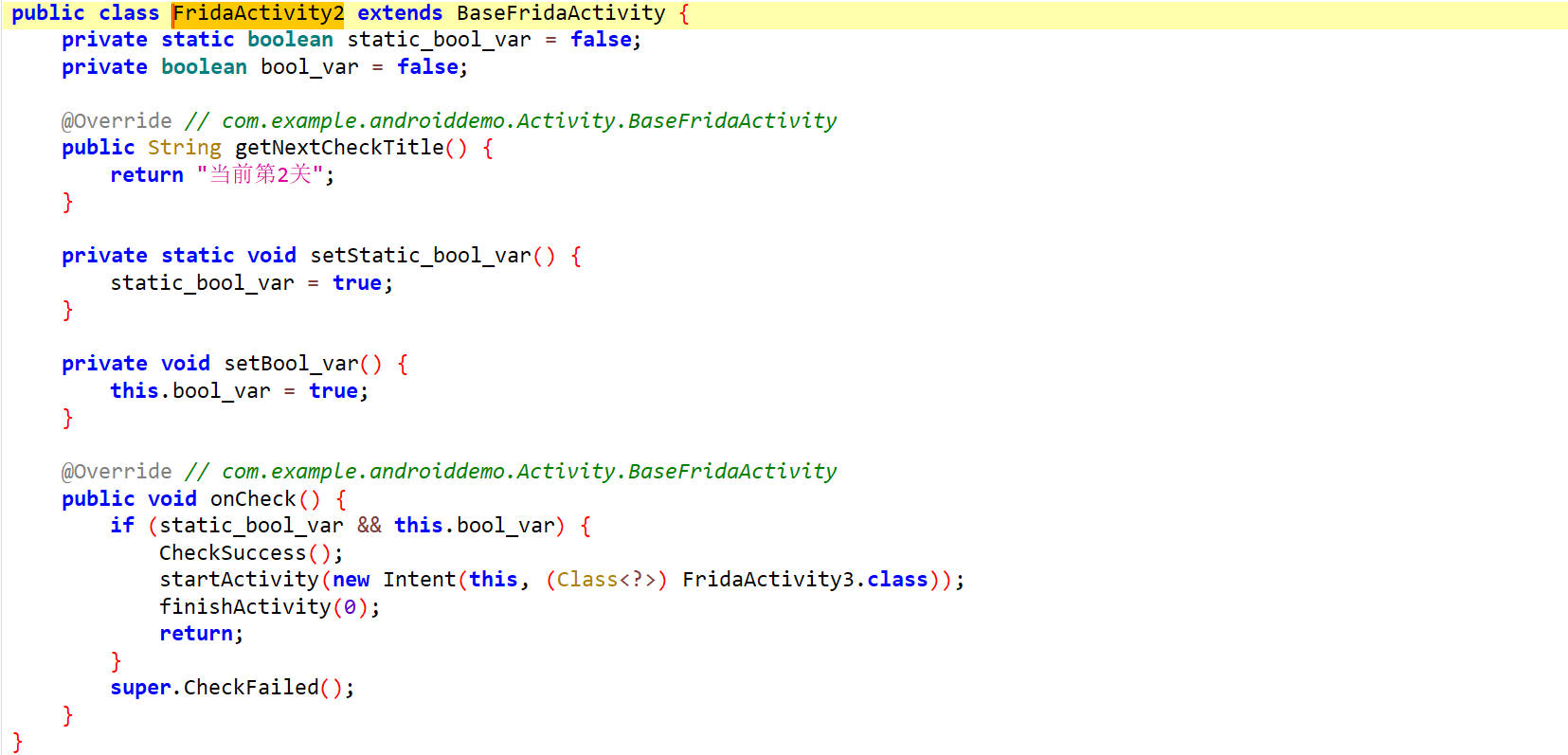
需要把static_bool_var和bool_var的值都修改为true才能进入FridaActivity3
这里可以主动调用setStatic_bool_var方法和setBool_var方法
1 | function hook_activity2(){ |
hook 结果
1 | static_bool_var: false |
点击进入第三关
第三关
第二关结束跳转到了FridaActivity3
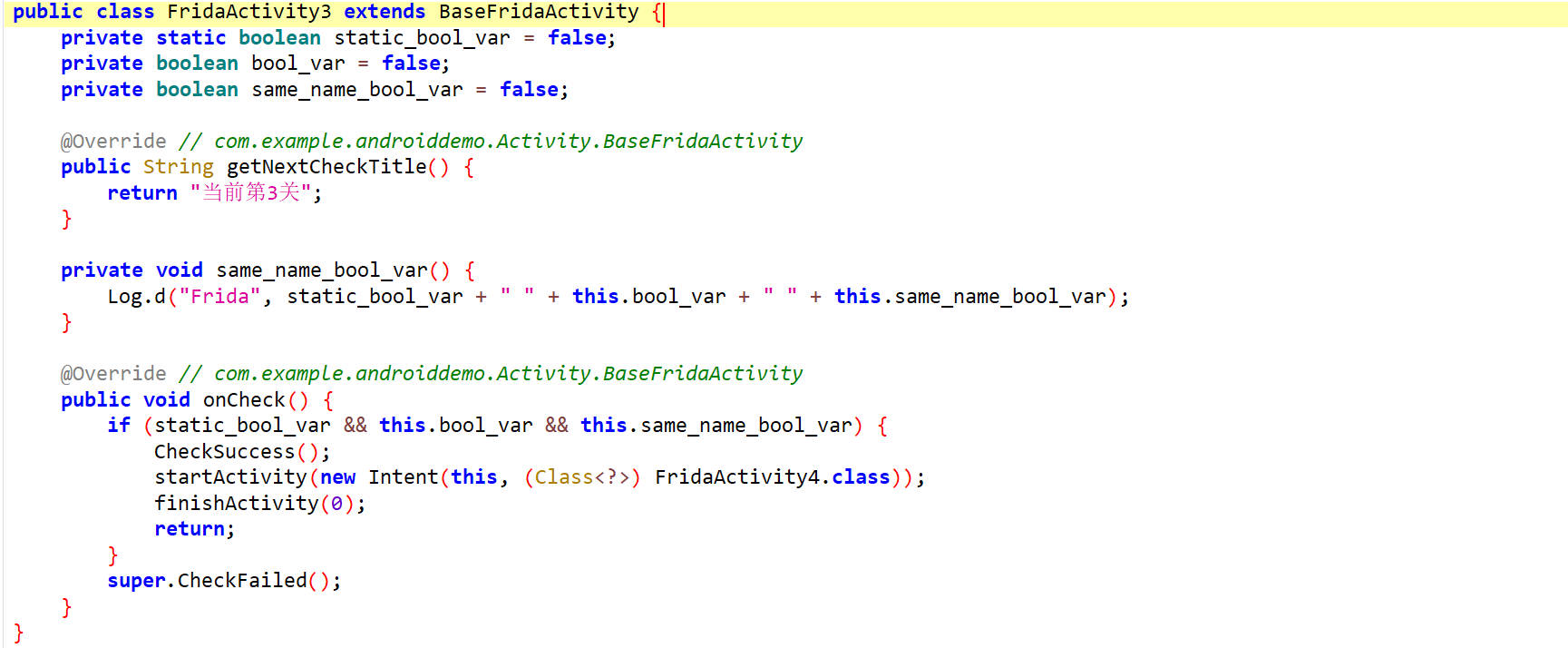
需要把static_bool_var、bool_var、same_name_bool_var三个值都设置为true才能进入FridaActivity4
这里存在一个坑点是存在一个与字段名same_name_bool_var相同的方法名same_name_bool_var,操作字段名的话需要在其名字前面加上一个_,即_same_name_bool_var
1 | function hook_activity3(){ |
hook 结果
1 | static_bool_var: false |
点击进入第四关
第四关
第三关结束跳转到了FridaActivity4
如下是第四关的源代码
1 | public class FridaActivity4 extends BaseFridaActivity { |
这里出现了内部类,需要把内部类中的方法返回值都设置为true
1 | function hook_activity4(){ |
点击进入第五关
第五关
第四关结束跳转到了FridaActivity5
查看check逻辑
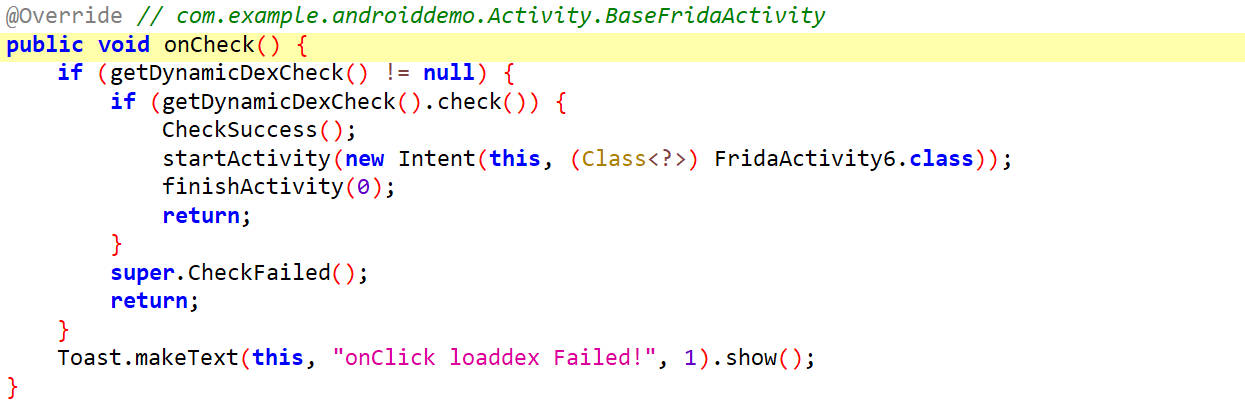
尝试hook check方法
1 | function hook_activity5(){ |
没有输出
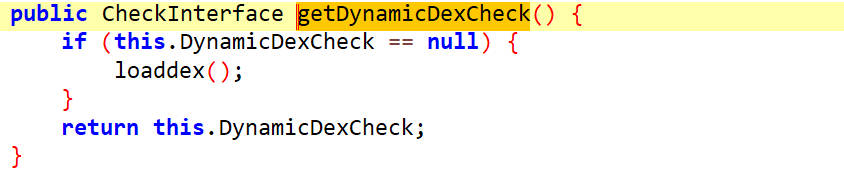
查看getDynamicDexCheck方法
hook getDynamicDexCheck
1 | function hook_activity5(){ |
hook 结果
1 | FridaActivity5.getDynamicDexCheck is called |
查看loaddex()方法
源码如下
1 | private void loaddex() { |
通过 DexClassLoader动态加载一个 .dex 文件(DynamicPlugin.dex),然后通过反射创建并实例化其中的一个类 com.example.androiddemo.Dynamic.DynamicCheck,并将其转换为 CheckInterface 接口的实例。
enumerateClassLoader()
枚举类加载器
1 | function enumclassLoader(){ |
hook 结果
1 | Found ClassLoader: dalvik.system.PathClassLoader[DexPathList[[directory "."],nativeLibraryDirectories=[/system/lib64, /system/lib64]]] |
dalvik.system.DexClassLoader就是要找的类加载器
修改DexClassLoader对check进行hook
1 | function enumclassLoader(){ |
hook结果
1 | enumclassLoader() |
点击进入第六关
第六关
第五关结束跳转到了FridaActivity6
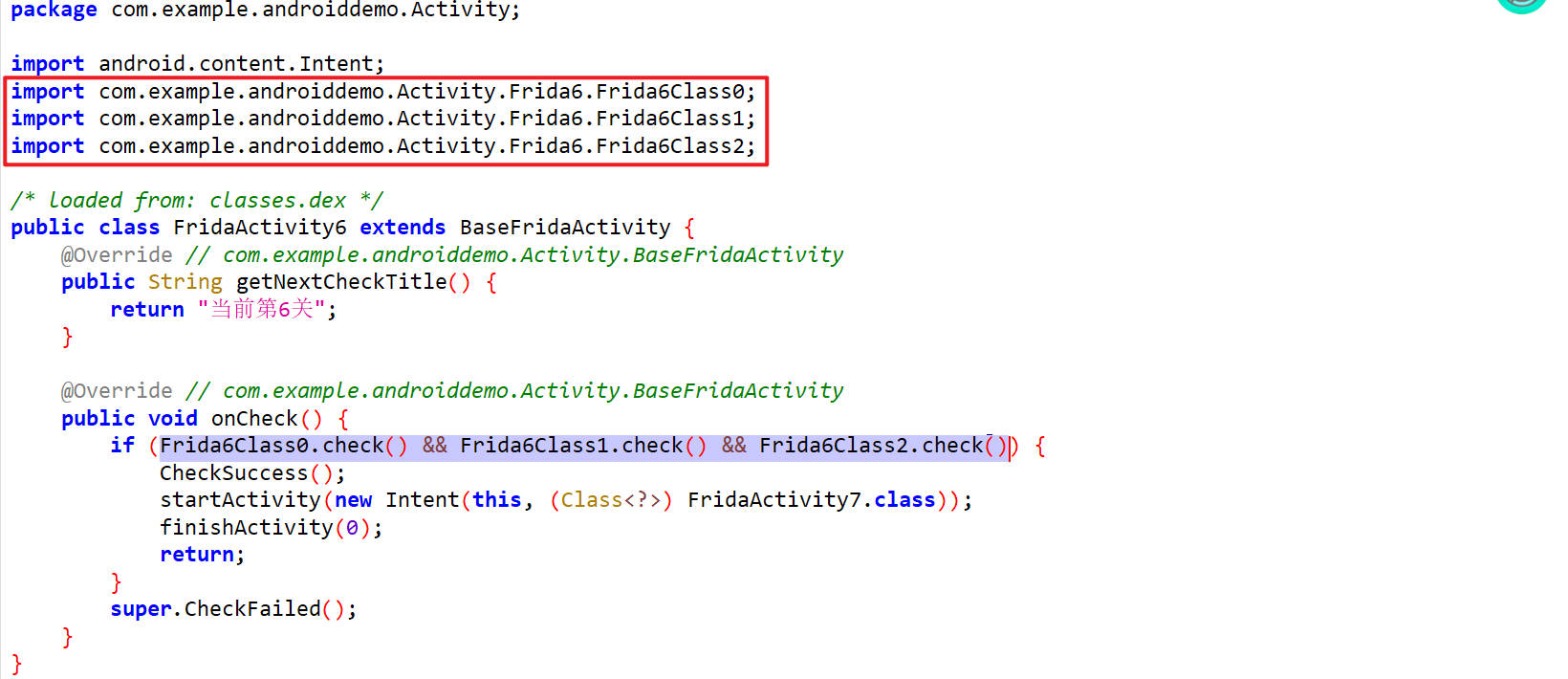
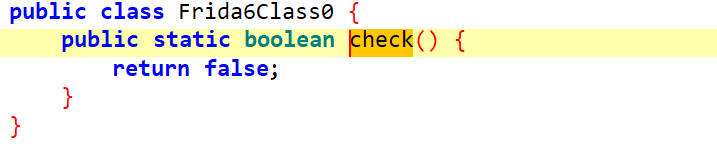
这里有三个check函数,他们的逻辑都是一样的,如下
hook check
1 | function hook_activity6(){ |
hook 结果
1 | Frida6Class0.check is called |