App信息
包名:com.toyota.ftmsApp

hook_dlopen()
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| function hook_dlopen(){
var android_dlopen_ext = Module.findExportByName(null,"android_dlopen_ext");
console.log("addr_android_dlopen_ext",android_dlopen_ext);
Interceptor.attach(android_dlopen_ext,{
onEnter:function(args){
var pathptr = args[0];
if(pathptr!=null && pathptr != undefined){
var path = ptr(pathptr).readCString();
console.log("android_dlopen_ext:",path);
}
},
onLeave:function(retvel){
console.log("leave!");
}
})
}
hook_dlopen()
|
输出
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
| Spawning `com.toyota.ftmsApp`...
addr_android_dlopen_ext 0x7e362e50ac
Spawned `com.toyota.ftmsApp`. Resuming main thread!
[Remote::com.toyota.ftmsApp ]-> android_dlopen_ext: /system/framework/oat/arm64/org.apache.http.legacy.odex
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/oat/arm64/base.odex
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libDexHelper.so
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libdexjni.so
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libmpaascpu.so
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libcrashsdk.so
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libAPSE_8.0.0.so
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libAPSE_J.so
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libmmkv.so
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libBaiduMapSDK_base_v7_6_0.so
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libdatabase_sqlcrypto.so
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libtiny_magic.so
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libAPMUOCPLIB.so
leave!
android_dlopen_ext: /data/app/com.google.android.webview-43dhvf0Cls2Vv-7QVhk2EA==/oat/arm64/base.odex
leave!
android_dlopen_ext: /data/user/0/com.toyota.ftmsApp/app_u4sdk/dlibs/71973616/lib/arm64-v8a/libwebviewuc.so
leave!
android_dlopen_ext: libmonochrome_64.so
leave!
android_dlopen_ext: /data/app/com.google.android.trichromelibrary_694313733-7b8EruQksFO0yRYXLSorCg==/base.apk!/lib/arm64-v8a/libmonochrome_64.so
leave!
android_dlopen_ext: /system/lib64/libwebviewchromium_plat_support.so
leave!
android_dlopen_ext: /vendor/lib64/hw/gralloc.sdm845.so
leave!
android_dlopen_ext: /vendor/lib64/hw/android.hardware.graphics.mapper@2.0-impl-qti-display.so
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libumeng-spy.so
leave!
android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libBugly_Native.so
leave!
Process terminated
[Remote::com.toyota.ftmsApp ]->
Thank you for using Frida!
PS D:\fridajs>
|
这里面的libDexHelper.so就是梆梆的特征
打印它的线程
hook_pthread()
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
| function hook_dlopen(){
var android_dlopen_ext = Module.findExportByName(null,"android_dlopen_ext");
console.log("addr_android_dlopen_ext",android_dlopen_ext);
Interceptor.attach(android_dlopen_ext,{
onEnter:function(args){
var pathptr = args[0];
if(pathptr!=null && pathptr != undefined){
var path = ptr(pathptr).readCString();
if(path.indexOf("libDexHelper.so")!=-1){
console.log("android_dlopen_ext:",path);
hook_pthread()
}
}
},
onLeave:function(retvel){
}
})
}
function hook_pthread() {
var pth_create = Module.findExportByName("libc.so", "pthread_create");
console.log("[pth_create]", pth_create);
Interceptor.attach(pth_create, {
onEnter: function (args) {
var module = Process.findModuleByAddress(args[2]);
if (module != null) {
console.log("address", module.name, args[2].sub(module.base));
}
},
onLeave: function (retval) {}
});
}
function main(){
hook_dlopen()
}
main()
|
输出
1
2
3
4
5
6
7
8
9
10
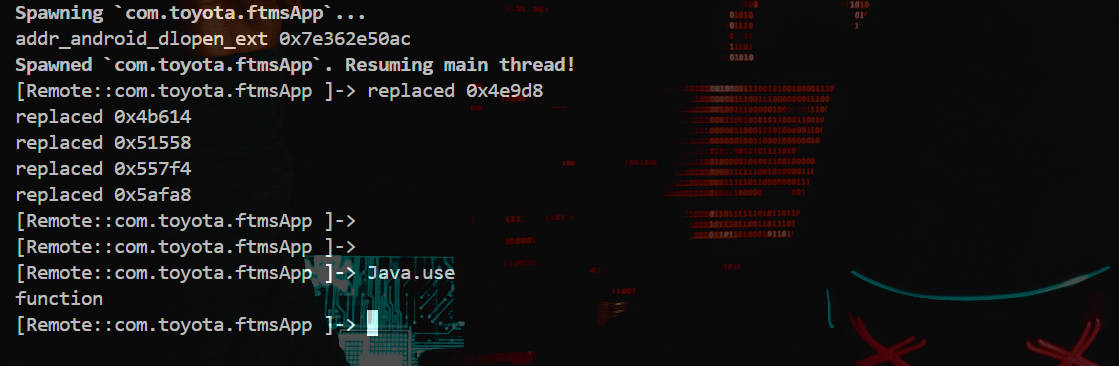
| Spawning `com.toyota.ftmsApp`...
addr_android_dlopen_ext 0x7e362e50ac
Spawned `com.toyota.ftmsApp`. Resuming main thread!
[Remote::com.toyota.ftmsApp ]-> android_dlopen_ext: /data/app/com.toyota.ftmsApp-Hz8olRrK9-kq0uBKLar_0g==/lib/arm64/libDexHelper.so
[pth_create] 0x7e34a8eb64
Process terminated
[Remote::com.toyota.ftmsApp ]->
Thank you for using Frida!
PS D:\fridajs>
|
相关线程信息还没打印出来就挂了
clone
了解到pthread_create里会调用一个clone()这个更底层的函数,对这个函数进行hook
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| function hook_clone(){
let clone = Module.findExportByName("libc.so","clone");
Interceptor.attach(clone,{
onEnter:function(args){
console.log("func address:",args[0]);
var module = Process.findModuleByAddress(args[0]);
if (module){
console.log("func in module:",module.name);
}else{
console.log("not find!")
}
},
onLeave:function(retcal){
}
})
}
hook_clone()
|
输出
1
2
3
4
5
6
7
| Spawned `com.toyota.ftmsApp`. Resuming main thread!
[Remote::com.toyota.ftmsApp ]-> func address: 0x7e34a8f07c
func in module: libc.so
func address: 0x7e34a8f07c
func in module: libc.so
func address: 0x7e34a8f07c
func in module: libc.so
|
打印调用栈
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
| function hook_clone(){
let clone = Module.findExportByName("libc.so","clone");
Interceptor.attach(clone,{
onEnter:function(args){
console.log("func address:",args[0]);
var module = Process.findModuleByAddress(args[0]);
if (module){
console.log("func in module:",module.name);
console.log(`native stack:}`);
console.log(Thread.backtrace(this.context, Backtracer.ACCURATE).map(DebugSymbol.fromAddress).join('\n') + "\n");
}else{
console.log("not find!")
}
},
onLeave:function(retcal){
}
})
}
hook_clone()
|
输出
1
2
3
4
5
6
7
8
9
10
| Spawned `com.toyota.ftmsApp`. Resuming main thread!
[Remote::com.toyota.ftmsApp ]-> func address: 0x7e34a8f07c
func in module: libc.so
native stack:
0x7e34a8ede0 libc.so!pthread_create+0x27c
func address: 0x7e34a8f07c
func in module: libc.so
native stack:
0x7e34a8ede0 libc.so!pthread_create+0x27c
|
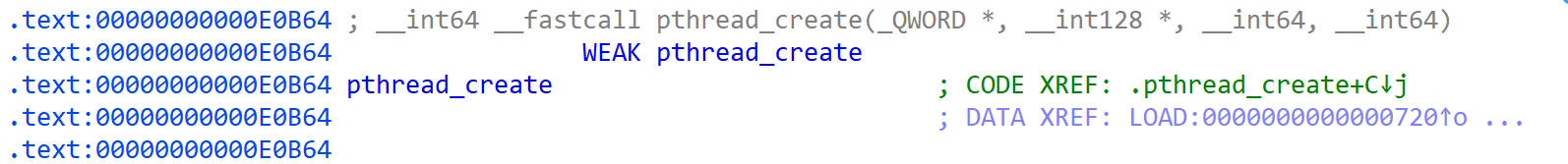
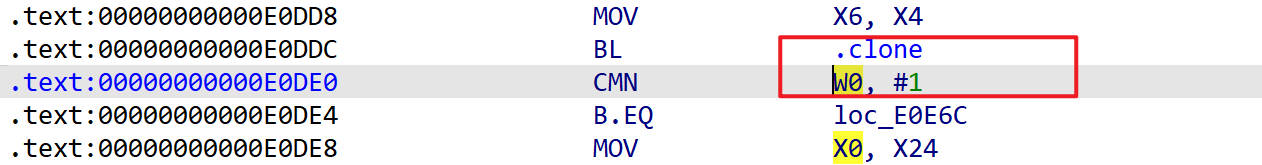
用IDA打开libc.so跳转到pthread_create+0x27c这个地方看看
先找到pthread_create的地址0xE0B64
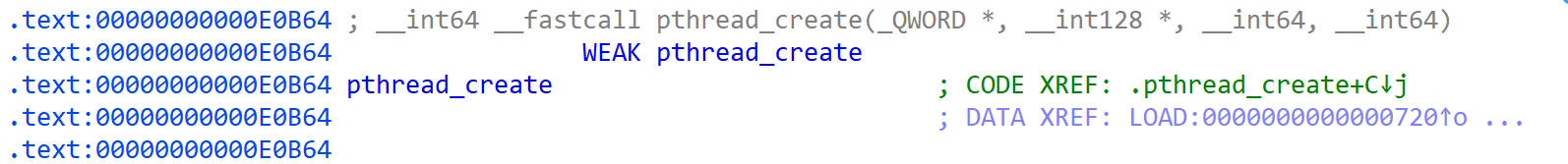
0xE0B64+0x27C=0xE0DE0
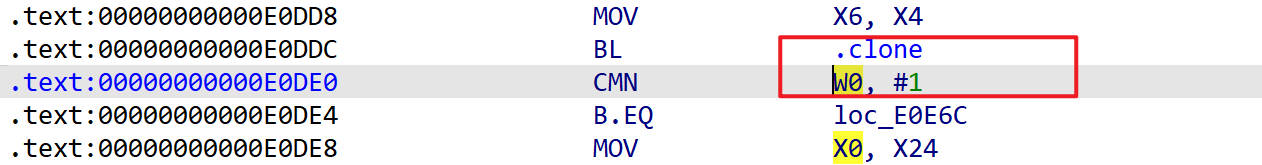
反汇编后如下
这里调用的是clone函数
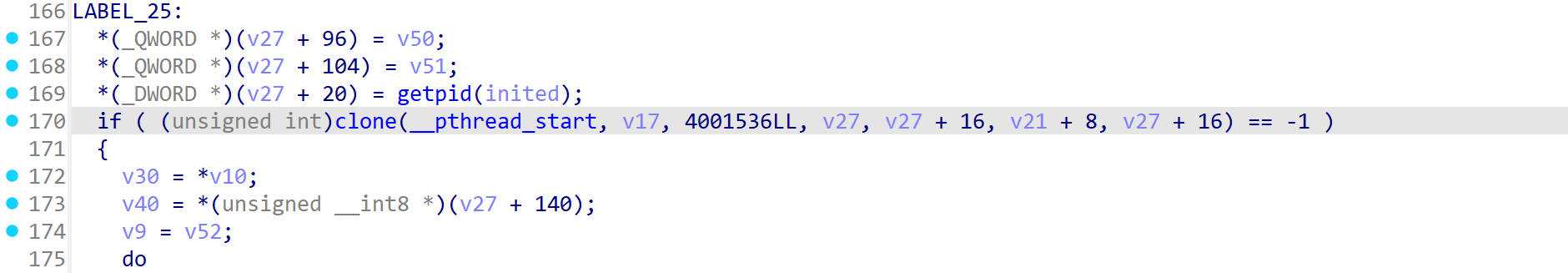
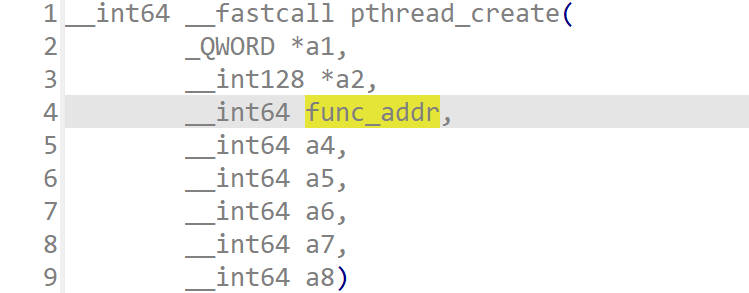
我们知道pthread_create()函数的第3个参数是线程函数指针,在这里我们跟一下这个参数是怎么走的
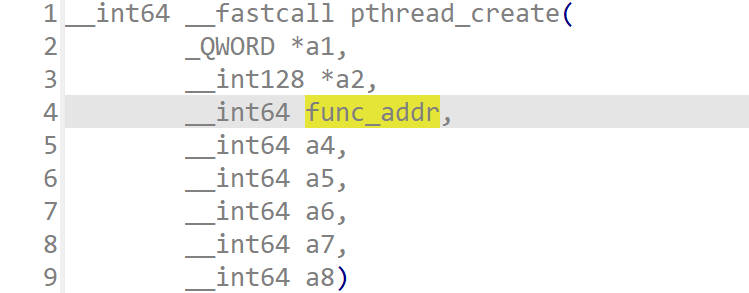
参数重命名为func_addr
先是赋值给了v50,如下
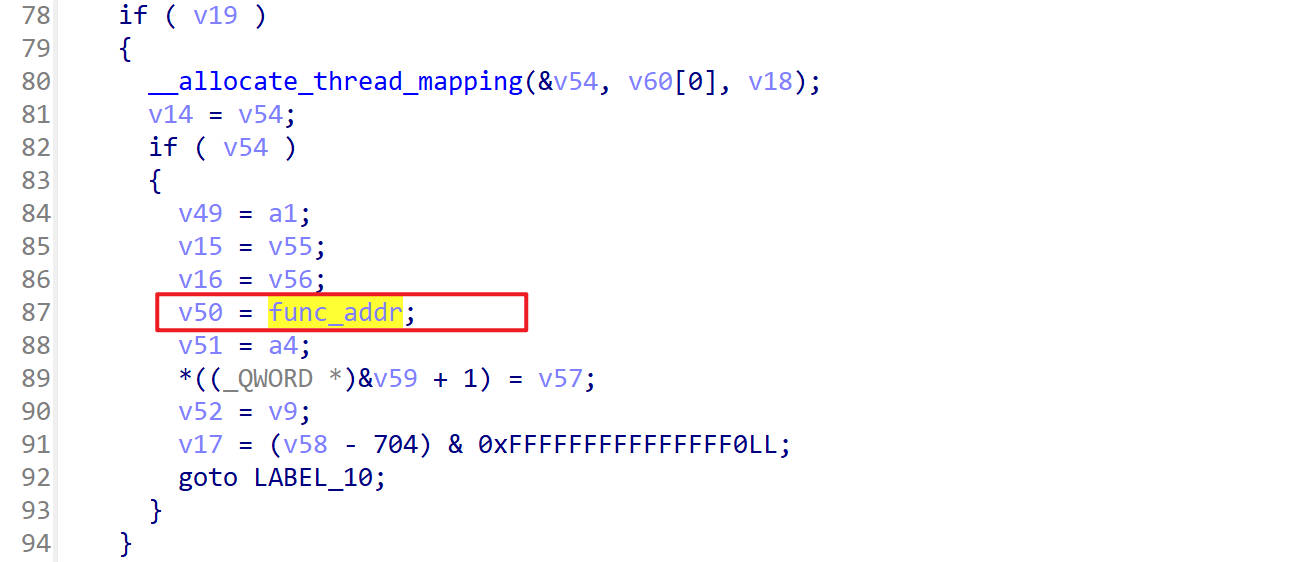
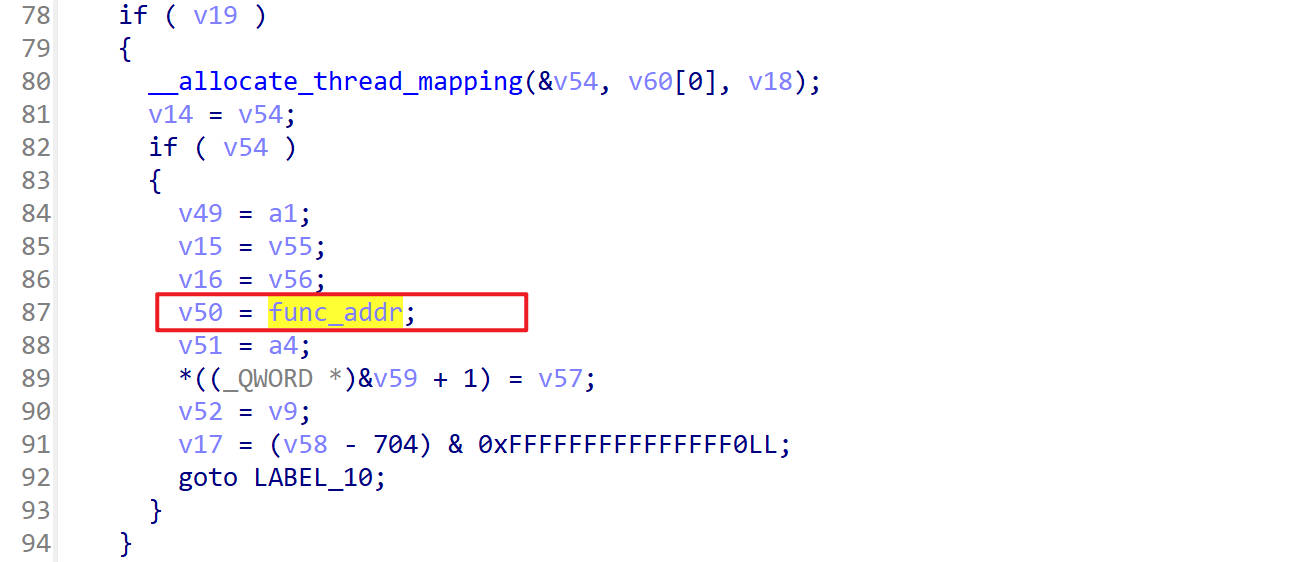
然后v50赋值给了v27+96
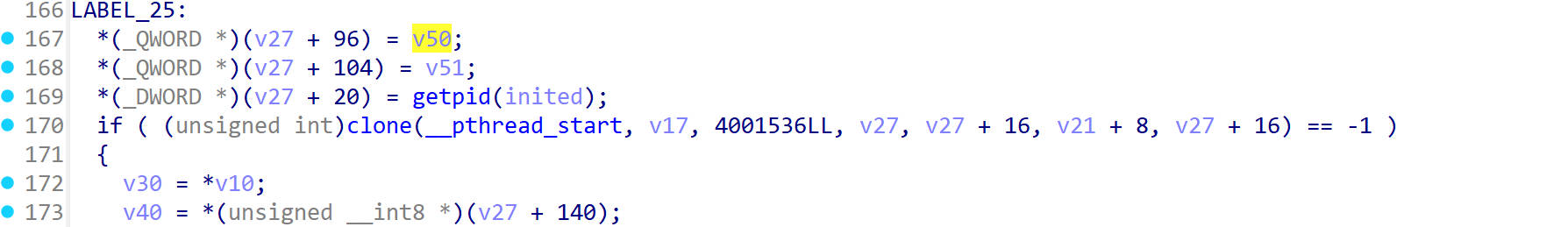
这里clone函数的第四个参数就是v27,我们把它+96,就可以拿到线程函数的地址了
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
| function hook_clone(){
let clone = Module.findExportByName("libc.so","clone");
Interceptor.attach(clone,{
onEnter:function(args){
if(args[3]!=0){
let addr = args[3].add(96).readPointer();
var module = Process.findModuleByAddress(addr);
if (module){
console.log("func in module:",module.name,"offset:",addr.sub(module.base));
}else{
console.log("not find!")
}
}
},
onLeave:function(){
}
})
}
hook_clone()
|
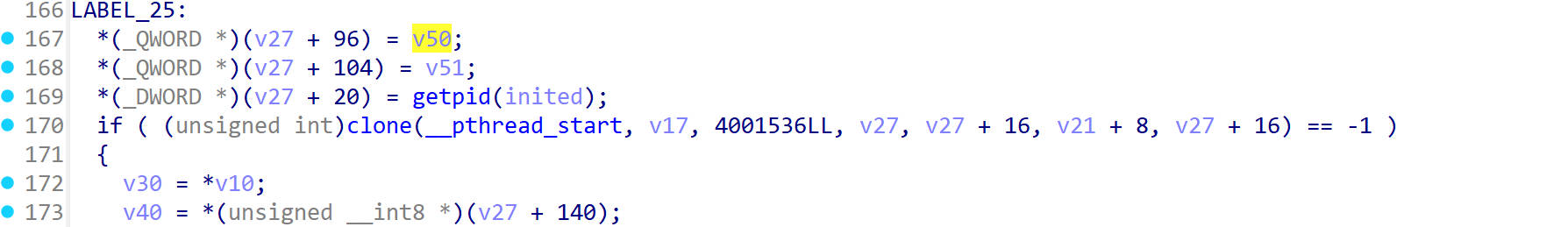
输出
1
2
3
4
5
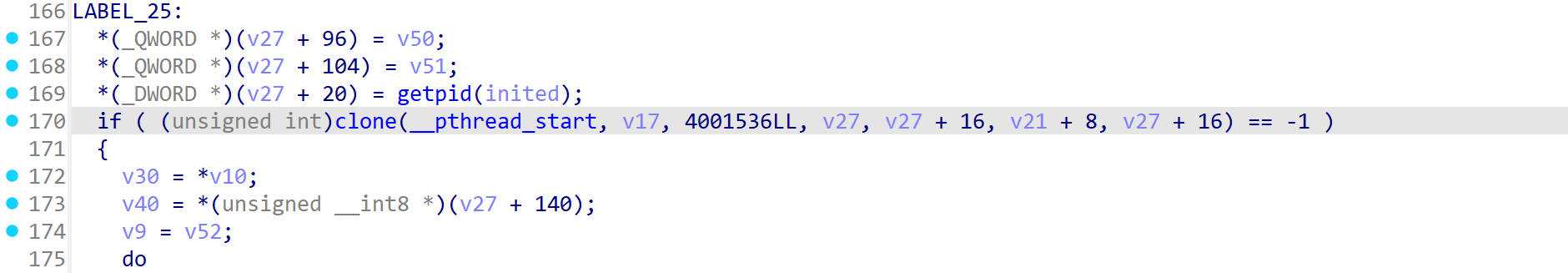
| func in module: libDexHelper.so offset: 0x4e9d8
func in module: libDexHelper.so offset: 0x4b614
func in module: libDexHelper.so offset: 0x51558
func in module: libDexHelper.so offset: 0x557f4
func in module: libDexHelper.so offset: 0x5afa8
|
nop
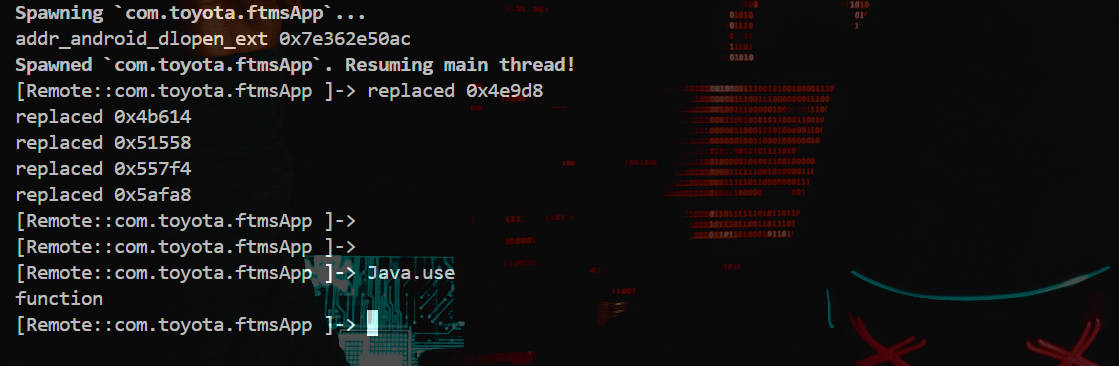
然后把这些地址nop一下
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
| function nop_addr(addr) {
Memory.protect(addr, 4 , 'rwx');
var w = new Arm64Writer(addr);
w.putRet();
w.flush();
w.dispose();
}
function hook_dlopen(){
var android_dlopen_ext = Module.findExportByName(null,"android_dlopen_ext");
console.log("addr_android_dlopen_ext",android_dlopen_ext);
let match = false;
var listener = Interceptor.attach(android_dlopen_ext,{
onEnter:function(args){
var pathptr = args[0];
if(pathptr!=null && pathptr != undefined){
var path = ptr(pathptr).readCString();
if(path.indexOf("libDexHelper.so")){
match = true;
}
}
},
onLeave:function(){
if(match){
var module = Process.findModuleByName("libDexHelper.so");
if(module!=null){
nop_addr(module.base.add(0x4e9d8))
console.log("replaced 0x4e9d8")
nop_addr(module.base.add(0x4b614))
console.log("replaced 0x4b614")
nop_addr(module.base.add(0x51558))
console.log("replaced 0x51558")
nop_addr(module.base.add(0x557f4))
console.log("replaced 0x557f4")
nop_addr(module.base.add(0x5afa8))
console.log("replaced 0x5afa8")
match = false;
listener.detach()
}
}
}
})
}
hook_dlopen()
|
ok了如下